Locks, Seals, Security Cameras for Ballots
Locks, seals and security
cameras
Evaluations and standards for locks
Commentary on locks in different states
State rules for seals and locks
State rules for action on missing or extra ballots
Guidelines for ballot security
Insiders have keys. They don’t need to pick locks. Short
sentences for breaching storage.
Election crimes have short sentences
Page uses Atkinson Hyperlegible font
from Braille Institute
Locks, seals and security cameras
Locks,
seals and security cameras keep out unskilled thieves and accidental access.
Therefore they matter a great deal. However, they are not a barrier to skilled
attackers or wealthy dishonest interests, domestic or foreign, which are
willing to hire skilled attackers.
Ballots
are not the only election materials that must be stored securely. Paper and
electronic pollbooks, access logs, seal numbers, and equipment are among other
crucial items which require secure storage.
Basic facts
Security features of election
offices vary.
Outside doors always have locks, like any government office. Sometimes they
have multiple locks and guards. Storage rooms also usually have one or two
locks. Even file cabinets to store election records and seal logs can have two
locks. In big counties, the central election computers are locked in a
separate room, where only a few staff go, often with non-opening windows for
public observation. Issues include who has keys, and how hard it is to
duplicate keys or pick the locks. Electronic locks keep a log of who enters.
Issues include who programs the lock and its keys, year after year, who can
access the logs, and whether it has a traditional key lock to bypass the
electronics.
Ballot
boxes vary too. There are ballot boxes or heavy bags in polling places to store
voted ballots. An office may use the same containers for longterm
storage, or may store ballots in cardboard boxes and keep the precinct boxes or
bags empty for the next election. Ballots which include federal races must be
stored for 22 months, by federal law. Other ballots are usually stored for a
few months, by state law.
Ballot
boxes may have one or more locks, with keys held by different people. They
often have seals, such as custom-printed, numbered zip ties, metal &
plastic seals, or adhesive labels which show who sealed the box and when. It is
common, but not universal, to put a seal on ballot boxes before they leave the
voting location, and, for ballots scanned centrally, to seal them after they
are scanned, so they are not accidentally picked up and  scanned again. Some ballots
sit on shelves unsealed. Seals are not intended to be tamper-proof, but rather
tamper-evident, meaning that someone
looking at them should be able to tell if the seal has been compromised.
scanned again. Some ballots
sit on shelves unsealed. Seals are not intended to be tamper-proof, but rather
tamper-evident, meaning that someone
looking at them should be able to tell if the seal has been compromised.
Avoiding suspicion
The
public knows that locked, sealed ballots and other records are not perfectly
safe. We still deserve to know how well security systems are set up.
Many
people will be suspicious if you take a close interest in election locks, seals
and cameras. You’d be 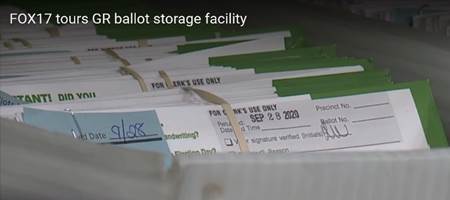 suspicious yourself if
someone wanted details about the locks on your home.
suspicious yourself if
someone wanted details about the locks on your home.
Learning
about locks, seals and cameras may be best done by a formal group, filing
public records requests (FOIA) for brands of locks and cameras, lists of keys
issued, logs of electronic locks, old camera footage, and protocols for the
office monitoring the cameras. That way no one is personally snooping and
subject to arrest or harassment. See https://www.nfoic.org/organizations/
on public records requests. You can often attend poll worker training or read
copies of poll worker manuals, where the office tells poll workers how to
handle seals. Sometimes an internet search will find local poll worker manuals,
or you can ask the election office for them. We keep a collection of links to pollworker manuals,
and we’ll appreciate if you add a link to any other manual you find, to
help other volunteers.
Locks
Examples
of issues with locks
A
good warning about how easily a skilled
person can pick any lock is in https://www.youtube.com/embed/ULUz4u5FLYg?start=74&end=179
where he picks 7 locks in 1 minute 45 seconds.
Lockpicking is widely taught and practiced:. "The
Strange Things That Happen at a Lock-picking Convention".. Lockpicking
is a legal sport: https://en.wikipedia.org/wiki/Locksport
A
locksmith can improve locks
a great deal, at low cost: https://www.youtube.com/watch?v=7JlgKCUqzA0
“an
expert safecracker could break into just about any commercial vault in less
than 20 minutes” https://www.theatlantic.com/magazine/archive/2020/06/edward-snowden-operation-firstfruits/610573/
"Roger
Johnston... has conducted vulnerability
assessments on more than a thousand physical security and nuclear safeguard
devices, systems, and programs. It’s his opinion that all security technologies
and devices can be defeated—usually 'fairly easily'... http://losspreventionmedia.com/insider/retail-security/physical-security-threats-and-vulnerabilities/
●
"The
typical security manufacturer isn’t likely to have good insider threat
security, so product tampering at the source is a risk...Then [the security
device] will sit on loading docks, and then sit again, sometimes for months,
somewhere at the end user, and only then is it installed" said Johnston.
"But no one knows what the interior is supposed to look like, and
manufacturers don’t supply pictures, so it’s impossible to tell signs of
tampering." (also applies to security cameras)
●
...
"The problem at a lot of organizations is that they’re afraid to encourage
employees to think about these kinds of things, and they’re also afraid of what
they’ll find... many don’t want to see the expensive technology they bought
easily compromised... Looking at your security devices from the perspective of
attackers will always point out flaws... acknowledge that they are a
possibility... And appreciate which threats devices can and can’t protect
against." (also
applies to security cameras)
Access to locked courthouses wired.com/story/inside-courthouse-break-in-spree-that-landed-two-white-hat-hackers-in-jail/
●
"gained
access to the building’s server room, and even found that a judge had left
their computer open and unlocked on their bench at the front of a courtroom.
Underneath the laptop, for good measure, was a sticky note with a password
written on it...
●
hundreds
of white-hat hackers who work across the US as professional penetration
testers—the rare kind that perform physical intrusions rather than mere
over-the-internet hacking...
●
few
nights’ string of intrusions...
●
many
of the alarm systems they’d encountered in the past weren’t properly armed and
never actually dialed out to responders...
●
glaring
vulnerabilities in the security of the state’s judicial system. Those
vulnerabilities, they say, were swept under the rug...
●
Coalfire staffer had easily gotten
into a courthouse during daylight hours by impersonating a state IT worker.
Then he'd simply sat down and plugged a computer into the network...
●
They
snaked a tiny boroscope camera under doors to check
for alarms or security guards. They picked old-fashioned pin-and-tumbler locks
on doors and desk drawers with simple lock picking tools, finding key cards in
drawers and using them to get past other internal doors in the building. They
used DeMercurio’s cutting board shim trick and a tool that slides under a door
and reaches up to hook its inside handle. At one point they made clever use of
a can of compressed air—the kind meant for cleaning dust out of keyboards—to
trigger an infrared motion sensor: Angle the propellant gas through the door’s
crack to the sensor inside, and it registers as a temperature change, tricking
the sensor into believing a person had approached from within and unlocking the
door to let them out...
●
between
those windows and the building’s server room, there wasn’t a single locked
door...
●
the
Iowa judicial branch seems to have taken entirely the wrong lesson from the
whole Coalfire affair. A new set of precautions it
released last October forbids courthouse break-ins of the kind Coalfire performed entirely. Never mind that Coalfire’s testing revealed security flaws as basic as
unlocked doors and windows, ones that could be used to access highly sensitive
criminal justice information like juror identities and evidence. “They just
said ‘We’re obviously insecure, and now we’re going to make sure we never test
again,’”"
Frequency: There are no statistics on how
often criminals enter rooms undetected. Law
enforcement often does so, so ability to enter rooms undetected is widespread at
least in law enforcement and former law enforcement.
·
Electronic
Frontier Foundation: "Peekaboo,
I See You: Government Authority Intended for Terrorism is Used for Other
Purposes".
·
McGuire, Sneak and Peek Warrants-Necessary for our Safety...?
·
2002
http://www.congressionalresearch.com/RL31377/document.php
·
“In
FY2020... courts issued close to 20,000 such
30-day, delayed-notice search warrants, and approved extended delayed notice
beyond 30 days in more than 10,000 cases." https://crsreports.congress.gov/product/pdf/LSB/LSB10652
Creating a master key from any key
in a building,
such as a borrowed restroom key, has been known since 1850. Blaze, Matt. "Cryptology and Physical
Security: Rights Amplification in Master-Keyed Mechanical Locks"
"[F]ew institutions want to spend the money for robust
security... in a battle between convenience and security, convenience has a way
of winning." "Many
Locks All Too Easy To Get Past". New York Times, 1/23/2003.
 Attackers
can 3D-print key blanks
from a photo of the lock, if they have trouble finding the blanks: Burgess, Wustrow & Halderman; (2015). "Replication Prohibited: Attacking Restricted Keyways with 3D-Printing"
Attackers
can 3D-print key blanks
from a photo of the lock, if they have trouble finding the blanks: Burgess, Wustrow & Halderman; (2015). "Replication Prohibited: Attacking Restricted Keyways with 3D-Printing"
Electronic
locks can
have different techniques:
● There is often a pickable
key lock to bypass the electronic system, as in the photo
●
Menn. "Exclusive:
High-security locks for government and banks hacked by researcher"
●
Millions
of electronic
locks vulnerable. 36% patched
● Greenberg "Inside an Epic
Hotel Room Hacking Spree"
●
Electronic locks using bluetooth
to measure proximity can be fooled by electronic relays near the lock and the
true key https://research.nccgroup.com/2022/05/15/technical-advisory-tesla-ble-phone-as-a-key-passive-entry-vulnerable-to-relay-attacks/
and https://www.schneier.com/blog/archives/2022/05/bluetooth-flaw-allows-remote-unlocking-of-digital-locks.html
Public
observers
When
you observe at an election office you may be able to note the following items.
- When and
where do they store ballots, seal logs & polling-place records?
- Does
anything have 2 locks, which both need to be unlocked to gain access?
- How many
locks are between the outdoors & the ballots?
- Do
hasps, hinges, seams look secure?
- What
brand are the locks?
Observing
the latter two of those may earn you suspicion. The last one above, and some
of the following may be subject to
public records requests. If you can find brand names, you can check for reviews
of their security, or YouTube videos of how easy they are to pick, and you can
suggest upgrades to officials.
- Who has
keys or electronic access?
- Does
anyone have all the keys or master key, to access alone?
- Who
programs electronic locks and their keycards?
- Who can
erase or change the logs of electronic locks?
- Can you
get the state or a college to evaluate locks, if you can find experts
there?
Seals
Video of children bypassing a
variety of seals
and putting the seals back in place https://www.youtube.com/watch?v=yaOVIFnoljo
New
Jersey:
Luther Weeks ctvoterscount.org/nj-chain-of-custody-six-unsuccessful-attempts-to-seal-voting-machines/
Seal
numbers:
The public is usually too far away to check seal numbers, though they could
compare old and new photos projected on a screen. Seal numbers and photos would
need their own secure storage.
How
to Choose and Use Seals.
by Johnston & Warner 2012 https://web.archive.org/web/20201031125201/https://alu.army.mil/alog/issues/JulAug12/Choose_Use_Seals.html An earlier, 2003, paper by
Johnston is at https://digital.library.unt.edu/ark:/67531/metadc933842/m2/1/high_res_d/976504.pdf
●
"Seal
manufacturers, vendors, and users typically overestimate the difficulty of
defeating their seals. At least 105 different generic methods are available for
potentially defeating a seal. These include, for example,
○
picking
the seal open without leaving evidence,
○
counterfeiting
the seal,
○
replicating
the seal at the factory,
○
changing
the serial number,
○
tampering
with the database of seal serial numbers,
○
drilling
into the seal to allow interior manipulation and then repairing the hole,
○
cutting
the seal and repairing the damage, and
○
not
installing the correct seal in the first place and then later replacing it with
the correct seal.
●
Full
counterfeiting is usually not the most likely attack on a seal unless the
adversary is perhaps attacking a large number of seals or has very limited time
to access the seal and its container…
●
no
seal is unspoofable (just as no lock is
undefeatable)... The optimal choice of a seal depends on the details of your
security goals, threats, and adversaries and your personnel... amateurs can
attack seals in a way that leaves little (and sometimes no) evidence...
●
Sometimes
the consternation and delays that a suspicious seal creates for superiors...
make front-line employees reluctant to raise their concerns."
Security
Seals on Voting Machines by
Andrew Appel, 2011 https://www.cs.princeton.edu/~appel/voting/SealsOnVotingMachines.pdf
●
When
seals are missing or broken, nothing usually can be done. "An attacker who
simply cuts, removes, or destroys tamper-indicating seals (without doing
anything else) can attempt to call the legitimacy of the election into
question...
●
it
must be difficult for the attacker to counterfeit a seal...
●
I
am not sure how much experience with injection-molding of plastics one needs to
be able to do this, but really that is rarely the point: in the vast majority
of cases there are much easier attacks—either the simple removal and
replacement of the original seal, or the purchase of extra (legitimate) seals
and changing their serial number, or the purchase of extra seals to re-use some
of their parts with the serial number of the original seal…
●
I
demonstrated for the judge the complete removal and replacement of all seals
with no visible evidence of tampering...
●
'To
the court’s untrained eye, most of the seals appeared unaltered with a few
showing minimal damage.' [Opinion 2010, p. 52]...
●
corrupt
election officials may hire corrupt seal inspectors... or deliberately fail to
train them... Consider an audit or recount of a ballot box, days or weeks after
an election...
●
The
tamper evident seals are inspected and removed—but by whom?...
●
the
public must be able to receive training on detection of tampering of those
particular seals."
Security cameras
Russia hacks security cameras: https://www.youtube.com/watch?v=idOpgrq9czc
Israel
hacks government security cameras in Iran https://www.timesofisrael.com/israel-linked-group-claims-cyberattack-that-shuts-down-70-of-irans-gas-stations/
Security
camera weaknesses in the US
are summarized byJohnston: https://losspreventionmedia.com/securitys-security/
“The typical security manufacturer isn’t
likely to have good insider threat security,” so product tampering at the
source is a risk...
●
Then
[the security device] will sit on loading docks, and then sit again, sometimes
for months, somewhere at the end user, and only then is it installed,” said
Johnston. “But no one knows what the interior is supposed to look like, and
manufacturers don’t supply pictures, so it’s impossible to tell signs of
tampering.” A skilled adversary can install a man-in-the-middle (MiM) attack or - (also applies to locks)
●
compromise
a device in some other way with just a few minutes of access, he noted.
●
Additionally,
security product design often facilitates tampering by using housing that is
thicker than necessary in order to make servicing devices easier. “So there is
all kinds of physical room inside it for someone to put in a device to capture
data and conduct MiM attacks. And end users don’t
usually go around and check for alien material inside their security devices,
so you have successful attacks,” said Johnston.
●
"The
problem at a lot of organizations is that they’re afraid to encourage employees
to think about these kinds of things, and they’re also afraid of what they’ll
find... many don’t want to see the expensive technology they bought easily
compromised... Looking at your security devices from the perspective of
attackers will always point out flaws... acknowledge that they are a
possibility... And appreciate which threats devices can and can’t protect
against." (also applies to locks)
"How
to hack a security camera. It's alarmingly simple". IFSEC.
"Official
Cybersecurity Review Finds U.S. Military Buying High-Risk Chinese Tech
(Updated)". Forbes.
"Hacking
Security Cameras – Schneier on Security".
Wireless
cameras can be jammed https://www.wxyz.com/news/how-criminals-are-using-jammers-deauthers-to-disrupt-wifi-security-cameras
An
alternative to camera monitoring is to connect intrusion sensors to a
transmitter which sends an “All OK” signal which stops when there is any
intrusion. It needs encryption to avoid spoofed signals. It can still be
spoofed by an insider who knows the encryption or can spoof the sensors.
Articles
on hacking security systems which depend on the widely used ZigBee wireless
transmission start on p.1 of http://rbsekurity.com/JPS%20Archives/JPS_15(1).pdf
Public
observers and cameras
Who watches
them?
Can you watch
them?
Will they
web-cast them?
Who can check
stored recordings?
How long are
recordings kept?
What brand
and model are the cameras? (Hikvision
is an example of a banned Chinese brand)
Can you get
the state or a college to evaluate cameras & storage?
It
may be worth asking for some footage under public records laws to see their
quality, and if they really exist.
As
noted earlier, requests by a formal group may be better received than from an
individual, so it is clear you want public information about the level of
security, and are not attackers. If you can find brand names, you can check for
reviews of their security, or youtube videos of how
easy they are to hack, and you can suggest upgrades to officials.
Standards and testing
Evaluations and standards for locks
These
groups do not give details of how stringent their tests are
- Consumer Reports lists “high security”
locks which are hardest to pick. Pay wall to see scores, but there are no
details on lock picking tests
- Sold Secure in Britain rates British
models, with Diamond being the best level
- Lockjudge collects comments from
other sites
- PC Magazine and CNET
ignore lock picking, other physical attacks, and hacks
- ANSI and BHMA
grades show ability to resist force, not lockpicking
- UL-437
describes methods to test locks, including picking (summary)
- Art-of-Lockpicking
reviews deadbolts, including pickability
8.
Consumer
Checkbook describes the types of non-commercial door locks (residential;
need commercial equivalent)
9.
Defense
Department has standards for physical security of arms and ammunition https://www.esd.whs.mil/Portals/54/Documents/DD/issuances/dodm/510076m.pdf
- GSA defines Class 5 and 6
containers https://www.gsa.gov/buy-through-us/purchasing-programs/requisition-programs/gsa-global-supply/national-stock-numbers/security-containers/types-of-security-containers
Commentary
on locks in different states
Colorado policies (under “County
Security Procedures”)
Connecticut
report 2021
New
York rules
Pennsylvania contractor assessed chain of custody
in 6 counties in 2021. The state keeps the report secret.
Philadelphia
report, 2019
Standards for seals
Federal
standards for seals apply to shipment, and medicine, none for storage.
●
http://everyspec.com/FED_SPECS/F/FF-S-2738A_25291/
Shipment seals must resist tampering for 30 seconds.
●
Manufacturers
must have third party testing and never make seals with the same design and
number. Buyers must check the manufacturer's security as well as their own. Dept of Homeland Security, User’s Guide on Security Seals for Domestic
Cargo January 2007 p/4-3, 6-9. https://www.hsdl.org/?view&did=235928
●
“A
tamper-evident package is one having one or more indicators or barriers to
entry which, if breached or missing, can reasonably be expected to provide
visible evidence to consumers that tampering has occurred... the package is
required to be distinctive by design
or by the use of one or more indicators or barriers to entry that employ an
identifying characteristic (e.g., a pattern, name, registered trademark, logo,
or picture). For purposes of this section, the term “distinctive by design” means the packaging cannot be duplicated
with commonly available materials or through commonly available processes. https://www.ecfr.gov/current/title-21/chapter-I/subchapter-C/part-211/subpart-G/section-211.132
There is extensive guidance at https://www.fda.gov/regulatory-information/search-fda-guidance-documents/cpg-sec-450500-tamper-resistant-packaging-requirements-certain-over-counter-human-drug-products
●
An
expert cannot find “ANY that would meet the requirement that they ‘…cannot be duplicated
with commonly available materials or through commonly available processes…’ ”
Johnston 2022 p.48 http://rbsekurity.com/JPS%20Archives/JPS_15(1).pdf
●
ASTM F1158-94 is a standard
for how hard it is to reapply a seal without detection
State rules for seals and locks
“legislation
on storage requirements is rare, storage is a key issue for local or state
officials… tamper-proof seals, cameras in equipment storage areas…“ https://web.archive.org/web/20221203112641/https://www.ncsl.org/research/elections-and-campaigns/election-security-state-policies.aspx
“No state has laws or regulations to ensure that the
paper trail is conserved adequately, and that evidence to that effect is
provided.” Bernhard et al. (2017). Public Evidence from Secret Ballots. in Electronic
voting : second International Joint Conference, E-Vote-ID 2017, Bregenz,
Austria, October 24-27, 2017, proceedings (PDF). Cham,
Switzerland. p. 122. ISBN 9783319686875. OCLC 1006721597.
"Election
officials should re-examine current practices for securing the chain of
custody of all paper ballots" ~US Senate Intelligence Committee
Alabama: lock equipment https://www.sos.alabama.gov/alabama-votes/voter/election-laws
Arizona: 1 lock https://www.azleg.gov/ars/16/00564.htm
California: 1 seal on ballot bag at
polling place (pp.19, 46) https://recorder.countyofventura.org/wp-content/uploads/2020/02/Poll-Worker-Handbook2-12-20.pdf
Connecticut: 1 lock, single
access http://ctelectionaudit.org/nov-2021-post-election-audit-report/
Colorado: 1 lock https://www.sos.state.co.us/pubs/info_center/laws/Title1/Title1Article7.html
Georgia: 1 lock & seal http://effinghamsheriff.org/DocumentCenter/View/4565/POLL-WORKER-MANUAL---May-2021
Kentucky: 3 locks for VBM https://apps.legislature.ky.gov/law/statutes/statute.aspx?id=51650
Maryland: 1 lock & seal http://www.montgomerycountymd.gov/elections/resources/files/pdfs/judge/chapter9.pdf
Michigan: 1 lock & seal https://www.michigan.gov/documents/sos/XII_Precinct_Canvass_-_Closing_the_Polls_266013_7.pdf
Minnesota: 1 lock https://www.revisor.mn.gov/statutes/cite/204B.40
New York: 2 locks held by 2 parties
https://www.newsday.com/news/region-state/election-voting-security-nassau-suffolk-1.50059036
and https://elections.erie.gov/PDFs/Election%20Day%20Manual%202021%20EPB%20Revised%20FINAL.pdf https://casetext.com/regulation/new-york-codes-rules-and-regulations/title-9-executive-department/subtitle-v-state-board-of-elections/part-6210-routine-maintenance-and-testing-of-voting-systems-operational-procedures-and-standards-for-determining-valid-votes/section-621011-voting-systems-security
North Carolina: 1 lock (public
photo of key) https://elections.nhcgov.com/wp-content/uploads/2020/10/2020-General-Election-Day-Voting-Training.pptx
Ohio: 1 lock & seal https://www.mcohio.org/20%20Mar%20PLS%20Class%201%20For%20Website.pdf
Pennsylvania: 1 lock https://delcopa.gov/vote/results.html
Texas: 1 lock election day, 2 locks
early votes, cameras https://www.sos.texas.gov/elections/laws/advisory2022-10.shtml
Utah: 1 lock https://kslnewsradio.com/1964619/follow-the-ballot-how-utahs-ballots-are-tabulated-and-audited/
West
Virginia: 2 locks held by 2 officials, usually of same party, sealed envelope http://www.wvlegislature.gov/wvcode/ChapterEntire.cfm?chap=3&art=3§ion=3
State rules for action on missing or
extra ballots
MI. state-wide: Kurth
and Oosting. "Records: Too many votes in 37% of Detroit’s precincts." Detroit News. When
ballot boxes don’t have the number of ballots expected, from paper records, the
original counts are accepted without checking.
WI. When Wisconsin
finds too few ballots in the ballot box, they recount the remaining short stack
of ballots and trust the result. When they find extra ballots stuffed in the
ballot box, they take out a random sample of all ballots from the box, to make
the numbers appear to match, without worrying about identifying the stuffed
ballots. Wisconsin Elections Commission, Election
Day Manual for Wisconsin Election Officials, July 2016, p. 101, http://elections.wi.gov/sites/default/files/publication/65/election_day_manual_july_2016_pdf_12281.pdf. And Ansolabehere et
al. 2018 Learning from Recounts https://www.liebertpub.com/doi/10.1089/elj.2017.0440
Drop boxes’ security
“Typically
made of heavy and high-grade metal, bolted to the ground,... locks,
tamper-evident seals… 24-hour video surveillance” https://www.cisa.gov/rumorcontrol
Collection
policies and form, San Luis Obispo, CA, 2022
Drop
boxes with scanner, Orange County CA 2022 https://ocvote.gov/press-releases/orange-county-ca-elections-to-pilot-additional-ballot-tracking-technology
Guidelines for ballot security
International groups
including Carter Center & Elections Canada: https://aceproject.org/ace-en/topics/vo/voc/voc03/voc03a
March 2023 EAC
·
When
offboarding an employee, cut off access to facilities and IT systems, including
changing physical locks, if necessary.
·
Change
keys or combinations on locks as necessary for each election.
·
Election
officials should move voting systems in a controlled transportation mode. In
other words, the equipment should be locked and sealed in the vehicle or
container before transport and unsealed at the delivery point. Sealing and
unsealing should be logged and completed only by election officials.
·
https://www.eac.gov/election-officials/election-management-guidelines
2018 Principles & Best Practices: https://electionaudits.org/files/Audit%20Principles%20and%20Best%20Practices%202018.pdf
“fully secured - Procedures regulating access to ballots and equipment could
include requiring signatures for access, documenting the reason for access,
preventing access by a single person, requiring that access be observed by
members of opposing parties, or using surveillance cameras to guard storage
areas.”
Foreigners and local storage
Besides
access to storage by local criminals (and possibly dishonest insiders),
foreigners are also a risk. NSA said, “a full-fledged nation-state attempt to
exploit your IT… include[s] not just remote stuff, but hands-on, sneak-into-your-house-at-night kind of stuff.”
Russia,
China and North Korea
are widely accused of using criminals to
act for them abroad and there is no reason other countries cannot do the
same:
- https://ecfr.eu/article/commentary_security_concerns_russian_mafia_back_on_agenda7083/
“For Moscow, Russian-based criminal networks provide an unconventional asset
in the geopolitical struggle with the West… At home and abroad, Russia’s
gangsters and spooks are often closely connected.”
- https://bpr.berkeley.edu/2019/12/16/gangs-and-gulags-how-vladimir-putin-utilizes-organized-crime-to-power-his-mafia-state/
"more and more crime networks tangentially linked to Russian actors
have appeared all over Europe. Multiple politically convenient
assassinations or assassination attempts have been made on anti-Russia
figures by gang members who have been accused of being Russian assets...
Russian government’s implicit support of the vast array of organized crime
means that the surge of activity across the European Union won’t be going
away any time soon."
- https://www.propublica.org/article/how-beijing-chinese-mafia-europe-protect-interests
“U.S. law enforcement has tracked interactions between Chinese government
operatives and Chinese American mobsters who harass dissidents, engage in
political interference and move offshore funds for the Communist Party
elite, U.S. national security officials say.”
- https://www.smh.com.au/national/illegal-malign-china-s-state-sponsored-crime-stretches-across-pacific-20230517-p5d8xe.html
“They’re [the Chinese government] leveraging these [criminal] groups to
undermine, again, our democracy... FBI had tracked “money flows … from the
organised criminal groups” in the Pacific to
“individuals within [the Chinese] government”... Five Eyes intelligence had identified
triad bosses who were working to corrupt powerful officials from Pacific
nations.”
- https://globalinitiative.net/wp-content/uploads/2017/09/TGIATOC-Diplomats-and-Deceipt-DPRK-Report-1868-web.pdf
“Much has been written about state-sponsored North Korean criminal
activity in Asia and Europe.”
- https://www.dni.gov/files/documents/NIC_toc_foldout.pdf
“North Korean entities maintain ties with crime networks to earn hard
currency.”
- https://nautilus.org/napsnet/napsnet-policy-forum/the-north-korean-criminal-state-its-ties-to-organized-crime-and-the-possibility-of-wmd-proliferation/
“I compared North Korea under Kim Jong Il with Serbia under Milosevic,
Romania under Ceausescu, and Panama under Noriega... Incidences of illicit
activity have occurred in every continent and almost every DPRK Embassy in
the world has been involved at one time or another.”Small
or no penalties:
Insiders have keys. They don’t need to pick locks. Short sentences for breaching storage.
MI 2022. Southfield MI city clerk pled no contest to
altering records of who voted, to hide that 193 ballots were not counted. Resigned;
no jail or probation time.
FL. 2017. Broward County(Fort Lauderdale) elections
staff erroneously destroyed ballots before the law allowed, and while a court
case for them was pending. Singhal "Order on Plaintiff's Motion for Summary Judgment."
Circuit Court of the 17th Judicial District. CACE17-010904(21) Friesdat. "Was the Heated 2016 Democratic Primary Rigged for Debbie
Wasserman Schultz?" Alternet. No penalties.
GA. 2017. statewide: Kennesaw State University, which
managed Georgia's elections, erased election records after a court case was
filed, and erased the backup after the case moved to federal court. Gumbel,
"Why US elections remain 'dangerously vulnerable' to
cyber-attacks." The
Guardian. No penalties.
MI. 2016, state-wide: Kurth and Oosting. "Records: Too many votes in 37% of Detroit’s precincts." Detroit News. No penalties
NV. 2016. Clark County (Las Vegas) Registrar of
Voters. RecountNow. "Report on the 2016 Presidential Recount in Clark County,
Nevada." Page 20. No penalties
CO. 2010. Saguache County Clerk accessed ballots for a
secret hand count. Weeks. http://www.ctvoterscount.org/foreign-policy-transparent-chain-of-custody/
She was recalled, but no legal penalties.
CA. 2007-2009. Cudahy city officials threw away,
uncounted, ballots for candidates running against city council members, as well
as accepting bribes. Gottlieb, Jeff , Hector Becerra and Ruben Vives
(2012-07-13). "Feds detail scale of graft in Cudahy".
Los Angeles Times. Councilman got 3
years in prison. Mayor got 1 year in prison. City manager got 5 years probation. (2013-02-27) Former Cudahy
councilman gets 3 years in extortion case Los
Angeles Times.
OH. 2004-2007.
Cuyahoga County (Cleveland) the third highest and a mid-level election
worker got 6 months probation for entering
ballot storage rooms in advance and secretly going through the ballots to make
public audits appear problem-free. In
court these staff "countered that the board had always done things that
way - with the knowledge of its attorney,"
Turner. "Elections board workers take plea deal."
Cleveland Plain Dealer. The election director had known about it and thought it
was OK, and was not charged. They pre-counted and left out of the random sample
precincts which had errors. Cuyahoga County Prosecutor 2005 via Black Box
Voting article 2007
KY. 2002-2007. Clay County election officials falsified
election results and destroyed forms which showed they helped voters, since the
voters they helped were being paid to vote certain ways. "US District Ct, ED KY, Indictment 09-16-Art US v.
Maricle, et al" and "Docket for United States v. Maricle, 6:09-cr-00016
- CourtListener.com". CourtListener. Initially sentenced to up to 26 years,
reduced after appeal to time served, up to 40 months in prison, plus 6
months home confinement for some. Final four defendants sentenced to time served in Clay
County corruption case Lexington
Herald Leader. Other Kentucky election frauds had similar sentences.
PA. 1993. Philadelphia election board did not keep
absentee ballots which had been rejected, from unregistered voters, and turned
them over to the campaign which collected them. "MARKS v. STINSON 19 F.3d 873 (1994)"
Stinson lost his seat in state Senate
Election crimes have short sentences
Federal
sentencing guidelines are short.
State sentences are also short, if they happen at all:
CA 2024 backlog of investigations of
campaign finance violations. https://calmatters.org/politics/elections/2024/10/campaign-finance-california-fppc-enforcement/
IA 2024 sentence of 4 months prison, 4
months home confinement, 2 years supervision, and $5,200 costs for wife of
county supervisor on 52 counts of ballot fraud. Federal judge “didn’t have previous cases
to set the bar for sentencing guidelines,” said sentencing guidelines were
18-24 months, but “he considered Taylor's lack of criminal record, significant
community support, and role as a caretaker for her family” Husband (county
supervisor) was unindicted co-conspirator. https://www.iowapublicradio.org/ipr-news/2024-04-02/prison-sentence-for-wife-of-woodbury-county-supervisor-federal-prosecutors-wanted-more
and https://www.ktiv.com/2024/04/01/kim-taylor-sentenced-eight-months-voter-fraud/
CT 2023 sentence of probation and
$35,000 fine for 28 counts of absentee ballot fraud in 2015 election. https://www.stamfordadvocate.com/news/article/Former-Stamford-Democratic-Party-chair-to-be-17578369.php
TX 2022 settlement of 1 year probation,
$2,000 fine and apology letter, dismissed 64 felonies in 2018 election. https://www.news-journal.com/news/elections/gregg-county-commissioner-pleads-guilty-to-misdemeanor-charge-in-election-fraud-case/article_0a07b022-7a27-11ec-a0af-83ef7cf20530.html
FL 2016. Miami campaign worker got probation
for filing false registrations https://www.miamiherald.com/news/local/crime/article163316298.html
FL 2016. Miami election worker got 2 years home confinement
and 3 years probation for adding votes to
absentee ballots in the office. https://www.miamiherald.com/news/politics-government/election/article111029767.html and https://www.telemundo51.com/noticias/local/sentenciada-una-mujer-acusada-de-fraude-electoral/23887/
OR 2012. Clackamas County election worker got
90-day sentence, $13,000 fine and community service for adding votes to
absentee ballots in the office. https://katu.com/archive/former-elections-worker-pleads-guilty-to-ballot-tampering-gets-90-days
